Ukraine has accused a Russian spy agency of carrying out a cyberattack intended to shut down part of its electricity grid, according to The Telegraph.
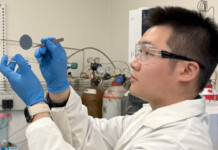
Russian hackers created customised malicious software intended to disconnect high-voltage substations belonging to a Ukrainian power company, the report said.
Related article: Russian Conti hackers claim CS Energy cyberattack
The country’s Computer Emergency Response Team, which defends against foreign hackers, said: “The idea of the attackers involved the decommissioning of several infrastructural elements.”
A malicious software “bomb” was scheduled to digitally detonate last Friday, the team said of the cyberattack. The bomb consisted of “wiper” malware that deletes all files on computers it infects.
This kind of malware has been used by Russia before but this is thought to be the first time since the February invasion where it has been used against critical infrastructure.
Slovakian cybersecurity company ESET, which helped the Ukrainians detect and remove the Russian malware, said its staff had seen “several destructive malware families” being deployed.
ESET says the malware gave the Russians access to the electricity company’s industrial control systems used to control equipment such as generators, switchgear and other critical equipment.
They are supposed to be well protected from outside access because of the severe consequences if a malicious party interferes with them.
Ukraine named the attackers as Sandworm—a well-known cybersecurity threat group. Sandworm has previously been identified by the Foreign Office as a unit of the Russian GRU spy agency called the Main Centre for Special Technologies.
Within Russia the centre is known as Unit 74455, the Foreign Office said in 2020.
Related article: Origin’s Beetaloo cleared over ties with Russian oligarch
The Ukrainian CERT said the Russian cyberattack had infiltrated the electricity generation company’s computer networks “no later than February 2022”, the month when Russia invaded Ukraine.
Read the full article here.